Dns
Doomsday and working of the internet
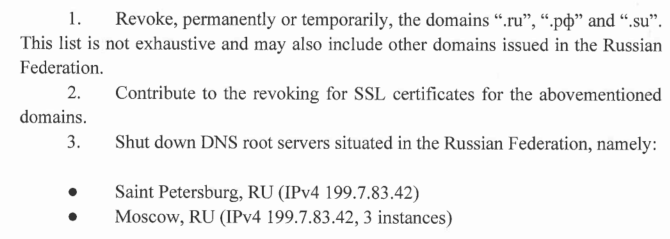
In the early phase of Russia - Ukraine war, Ukraine made a strange request to ICANN. They asked ICANN to remove .ru (Russian ccTLD) from the root DNS servers, revoke SSL certs for .ru and shut down root DNS servers hosted in Russia.
Here are the three requests they made:
Complete letter is here (and original source is here). This is going to be one of few notable cases where critical internet infrastructure is being weaponised. ICANN declined the request for good. Due to my limited understanding of Russia, Ukraine, US, EU, NATO etc I am not going to comment on the conflict itself. But coming to the critical infrastructure part - this reminds me of my earlier blog post on Doomsday and DNS resolution.
Doomsday and the DNS resolution
Last month I did a short webinar with Indian ISPs talking about DNS servers in detail. The idea of the session was to make network engineers from fellow ISPs familiar with root DNS servers, DNS hierarchy, anycast etc. As we went through slides it was clear from RIPE Atlas data that Indian networks are not reaching local DNS servers due to routing! (Data from RIPE Atlas here).
This may come as a surprise for policymakers (where there seem to be ongoing discussions around how India can have its own root DNS servers even though) we are not hitting existing local root DNS instances. Anyways does that statement of having own root DNS servers even possible?
Automated SSL certificate management for private containers
Lately, I have been playing with many tools and as one gets into deploying those tools, SSL comes as a pain point. A large number of web-based tools I use are internal and on a private network. VPN (with OSPF running over FRR) takes care of connectivity but still, it’s good to have SSL on these machines. Non-HTTPs websites are getting more & more ugly with browsers and even things like password managers do not fill the passwords anymore on their own for non-HTTPS websites.
DNSSEC deployment across the ccTLDs
While I am spending time on APNIC’s security workshop here at APNIC 46, I got curious about DNSSEC deployment across ccTLDs.
For those who may be unaware, DNSSEC adds signature the DNS responses making it possible to cryptographically verify a DNS query response.
Out of 254 ccTLDs, 125 support DNSSEC with a published DS record (at least that is what I get when I check their zone) and 129 do not support it as yet. So, for now, it is at 49.21%.
Encrypted DNS using DNSCrypt
Writing this post from my hotel room in Kathmandu. I found that many of the servers appear to be DNS resolvers which is unusual.
Have a look at these weird DNS replies:
dig @anuragbhatia.com . ns +short
a.root-servers.net.
b.root-servers.net.
c.root-servers.net.
d.root-servers.net.
e.root-servers.net.
f.root-servers.net.
g.root-servers.net.
h.root-servers.net.
i.root-servers.net.
j.root-servers.net.
k.root-servers.net.
l.root-servers.net.
m.root-servers.net.
dig @google.com . ns +short
b.root-servers.net.
c.root-servers.net.
d.root-servers.net.
e.root-servers.net.
f.root-servers.net.
g.root-servers.net.
h.root-servers.net.
i.root-servers.net.
j.root-servers.net.
k.root-servers.net.
l.root-servers.net.
m.root-servers.net.
a.root-servers.net.
This seems unusual and is the result of basically port 53 DNS hijack. Let’s try to verify it using popular “whoami.akamai.net” query.
Cloudflare hosting F root server
A few days some folks in internet community noticed Cloudflare AS13335 announcing F root server’s routes covering prefix 192.5.5.0/24.
dig version.bind ch txt @f.root-servers.net pic.twitter.com/YLW7hqt170
— Tony Finch (@fanf) April 3, 2017
Above tweet shows that case is clearly not a mistake but rather some sort of arrangement between Cloudflare and ISC (which is responsible for F-root). There was another discussion on DNS-OARC mailing list here. From our bgp.he.net tool, one can analyse route propagation for F root’s AS3557.
Being Open How Facebook Got Its Edge
An excellent presentation by James Quinn from Facebook on “Being Open How Facebook Got Its Edge” at NANOG68. YouTube link here and video is embedded in the post below.
Some key points mentioned by James:
- BGP routing is inefficient as scale grows especially around distributing traffic. They can get a lot of traffic concentrated to a specific PoP apart from the fact that BGP best AS_PATH can simply be an inefficient low AS_PATH based path.
- Facebook comes with a cool idea of “evolving beyond BGP with BGP” where they use BGP concepts to beat some of the BGP-related problems.
- He also points to fact that IPv6 has much larger address space and huge summarization can result in egress problems for them. A single route announcement can just have almost entire network behind it!
- Traffic management is based on local and a global controller. Local controller picks efficient routes, injects them via BGP and takes care of traffic balancing within a given PoP/city, balancing traffic across local circuits. On the other hand, Global PoP is based on DNS logic and helps in moving traffic across cities.
It’s wonderful to see that Facebook is solving the performance and load related challenges using fundamental blocks like BGP (local controller) and DNS (global controller). :)
Bangladesh .bd TLD outage on 18th August 2016
 Day before yesterday i.e on 18th August 2016 Bangladesh’s TLD .bd went had an outage. It was originally reported by Jasim Alam on bdNOG mailing list.
Day before yesterday i.e on 18th August 2016 Bangladesh’s TLD .bd went had an outage. It was originally reported by Jasim Alam on bdNOG mailing list.
dig btcl.com.bd @8.8.8.8
; <<>> DiG 9.10.4-P2 <<>> btcl.com.bd @8.8.8.8
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: SERVFAIL, id: 8114
;; flags: qr rd ra; QUERY: 1, ANSWER: 0, AUTHORITY: 0, ADDITIONAL: 1
;; OPT PSEUDOSECTION:
; EDNS: version: 0, flags:; udp: 512
;; QUESTION SECTION:
;btcl.com.bd. IN A
;; Query time: 76 msec
;; SERVER: 8.8.8.8#53(8.8.8.8)
;; WHEN: Thu Aug 18 14:24:25 Bangladesh Standard Time 2016
;; MSG SIZE rcvd: 40
His message shows that DNS resolution of BTCL (Bangladesh Telecommunications Company Ltd) was failing. Later Alok Das that it was the power problem resulting in outage. Let’s look ask one of 13 root DNS server about NS records on who has the delegation for .bd.
Host a RIPE Atlas probe!
RIPE NCC is running an excellent project called RIPE Atlas from few years. This is one of largest distributed network measurement projects where thousands of users host small devices called RIPE Atlas Probes on their networks, home connections, datacenters etc. These probes do measurement under both public and private category and make that data available publicly for use by network engineers and helps in optimizing routing. This page shows detailed coverage statistics of the probes.