Doomsday and working of the internet
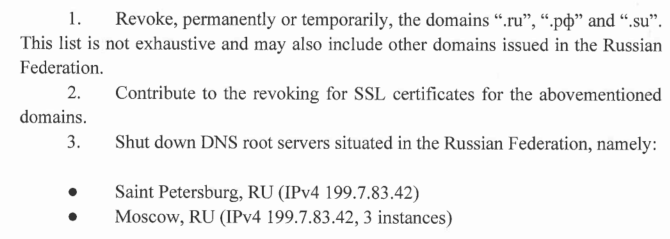
In the early phase of Russia - Ukraine war, Ukraine made a strange request to ICANN. They asked ICANN to remove .ru (Russian ccTLD) from the root DNS servers, revoke SSL certs for .ru and shut down root DNS servers hosted in Russia.
Here are the three requests they made:
Complete letter is here (and original source is here). This is going to be one of few notable cases where critical internet infrastructure is being weaponised. ICANN declined the request for good. Due to my limited understanding of Russia, Ukraine, US, EU, NATO etc I am not going to comment on the conflict itself. But coming to the critical infrastructure part - this reminds me of my earlier blog post on Doomsday and DNS resolution.
I wrote that post after hearing too many discussions, news articles etc about having a 14th root DNS server from India. It was a bad idea back then and it still is pointless. If we have a 14th root DNS server (from India), it is going to be an exact mirrored copy of the existing 13 root DNS servers. If even a single bit is forcefully altered, the cryptographic signatures would just fail and anyone doing DNSSEC validation would simply not resolve the DNS. If we run the 14th root DNS as an “Indian” one isolated from the world, it would just split the internet.
What makes current WAN “the internet”?
The super large WAN network is called the internet for three key technical assumptions:
- Network operators trust & have faith in RIRs
- Network operators trust each other technically by running BGP sessions & accepting prefix announcements
- All software implementations of DNS resolution trust 13 magical IPv4 and IPv6 addresses which belong to the root DNS server which starts the DNS resolution chain
Having the 14th server not in sync with the hidden master cluster administered by ICANN and managed by Verisign would result in a different version of the internet where “Google.com” may not be the Google Inc we know, where “microsoft.com” might not be the software giant we know.
I can imagine most of the discussions around the 14th root server as well as security are now going to come back after Ukraine’s letter across all Governments. Ukraine’s letter shows it’s not completely impossible that a country’s TLD is targeted.
While we should hope it never happens in theory in a war-like situation, .in ccTLD can be wiped out in the current setup. It’s always interesting to think of engineering solutions but this is going to be a very hard one because DNS (and BGP) are the fundamental layers of the core.
Is “DNS control” the only problem?
Let’s take a step back here and stop thinking about DNS. Are we fine otherwise? In the hypothetical case of war and assuming countries turn against each other, will the internet still work as we know it?
If enemy countries can go to extent of getting .in removed from the root zone, will they let Google, Facebook, Yahoo, Microsoft etc still function? Very likely not. Thus, in that case 90% of things an average person does over the internet (email, chat, videos, calls and whatnot) just won’t work.
It’s not possible to replace these services with an Indian alternate. We can hope more startups pop up across the world and we see more alternates but for now, it is what it is. Besides those key companies vanishing from the “Indian internet,” there can be a number of other things. SSL certificates issued by various (non-Indian) organisations can be revoked. RPKI ROA signatures of IP address prefixes can be revoked etc. There can be over a dozen of possible attack vectors, and kill switches in the current version of the public internet if a powerful state decides to use them. Thus it’s pointless to just protect the DNS (and that too with the flawed idea of the 14th root).
Buiding isolated networks
Since public internet cannot be guaranteed to work 100% time in an event of war. For policymakers, it would make much more sense to plan isolated networks all the way from layer 1 to layer 4 for critical establishments. These establishments can be defence forces, PMO, and various govt. ministries, HQ of various state Govt etc. It makes no sense in the current state to plan such a network for civilians.

To some extent layer 1, isolated networks do exist. Notice “NFS OFC” next time you are riding on a highway. That is “Network for Spectrum Optical Fibre Cable”. A private isolated network built for Indian defence forces. I have no idea of the software stack over there but to ensure the network is 100% isolated from any dependencies from outside, one can do things like:
- Use your own IP addressing. Just start with IPv6 with zero IPv4 fallback - No RIR dependency.
- Setup own DNS root servers geographically distributed across India - no root DNS dependency
- Setup own DNS resolvers pointed to these root DNS servers
- Setup own root CAs, setup Key Signing Key infra and issue TLS certificates from the ground up & inject root certs in all devices for such network
- Setup own internal RPKI infra from the trust anchor onwards
- Local oath authentication layer
- Setup the software components on top of it. This can basically email, chat, and video conferencing services to advanced nuclear command & control operations riding on top of such a private network
So with the fundamental idea that the Indian Govt. has control from layer 1 to layer 4, one can be certain that in an “act of war” this private infra cannot be easily targetted. Layer 4 is going to be the hardest here. One cannot write & maintain all software from scratch thus at layer 4, ultimately software part has to be used but carefully vetted for its dependencies to the outside world.
Furthermore, I think the above approach would be a better approach than embarrassing India on a global stage with a pointless 14th root server demand.