BSNL drops IP transit from BSCCL
Post on Google’s use of optical switching in it’s datacenter
Blog post about my good friend Shashank Dubey
Blog post covering Meta’s talk at NANOG 94 about use of XGS-PON in datacenter for management network
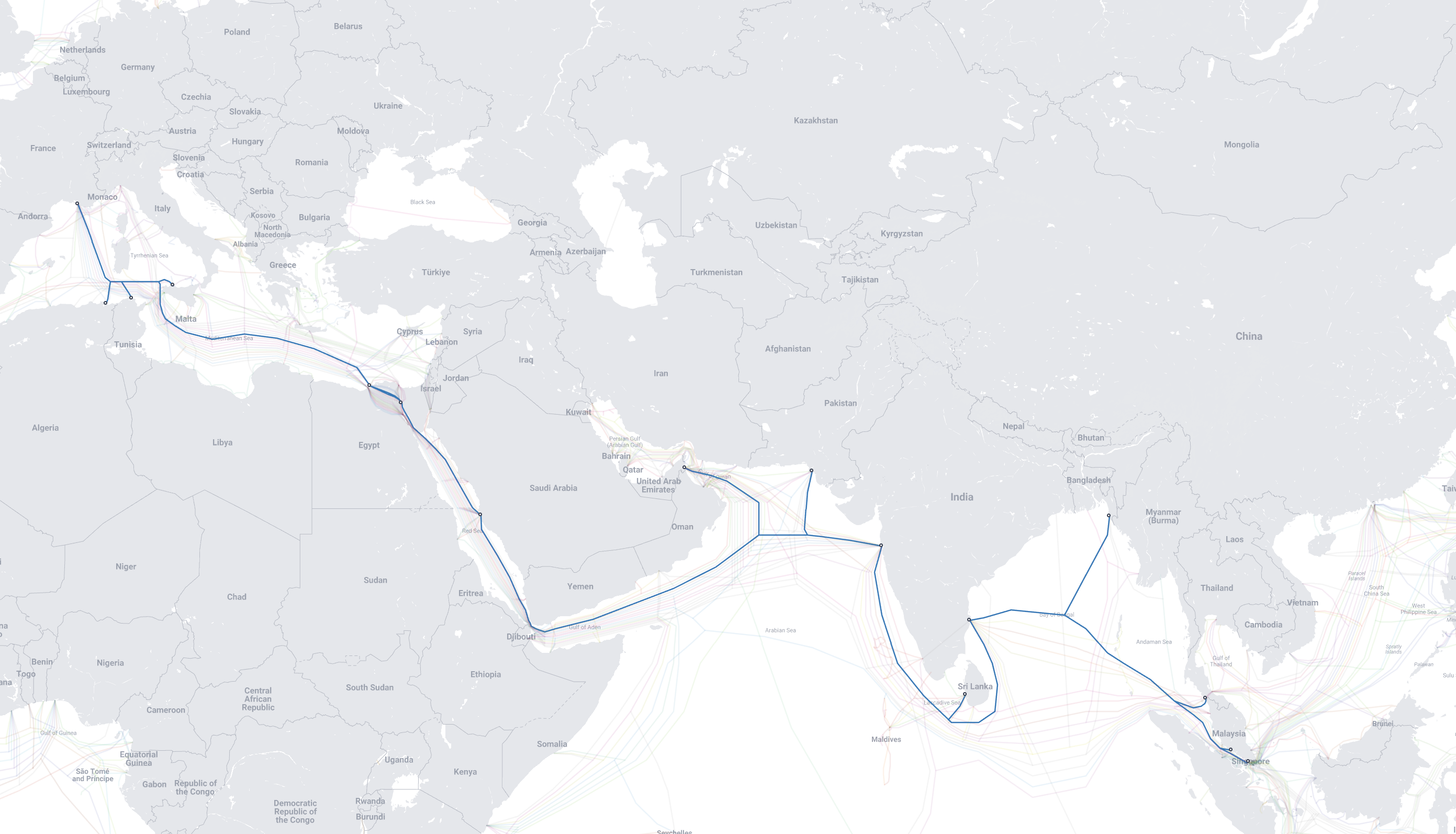
This post covers if we can detect impact of submarine cable cuts from BGP routing table.
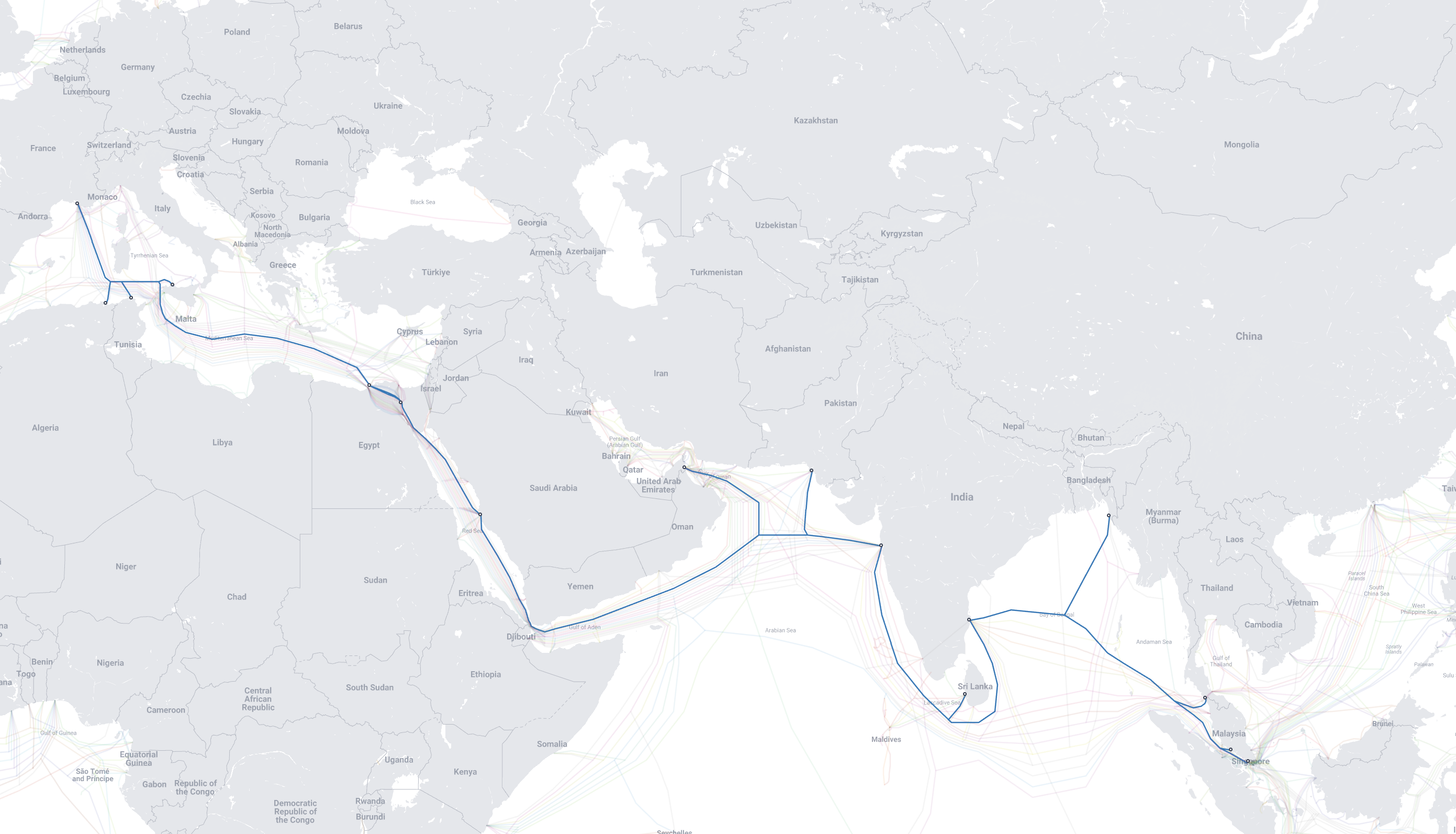
This is post about latency jump & packet loss between India and Europe due to submarine cable cuts at Jeddah
This post analyses how many nameservers of ccTLDs are anycasted
This post analyses upstream providers of Starlink in India
Blog post on erasure coding
Post covering hijack of 1.1.1.0/24 by AS4755